Points de contrôle
Set up a Service Account
/ 40
Create sink
/ 30
Configure Filebeat Google Cloud module
/ 30
Using Elastic Stack to Monitor Google Cloud
This lab was developed with our partner, Elastic. Your personal information may be shared with Elastic, the lab sponsor, if you have opted in to receive product updates, announcements, and offers in your Account Profile.
GSP992
Overview
In this lab, you will learn how to use the Elastic Stack to monitor Google Cloud. You will start by creating a simple Elasticsearch deployment using Elastic Cloud.
The goal of this lab will be to install and deploy Elasticsearch then use Beats, which are Elastic's lightweight data shippers, which sends operational data - logs and metrics - from systems and applications. You will use Beats to collect and monitor your services on Google Cloud.
What you'll learn
In this lab, you learn how to perform the following tasks:
- Create a deployment using Elastic Cloud
- Install and configure Beats to send data to Elasticsearch
- Use Kibana to visualize the ingested data
Prerequisites
This is an introductory level lab. No prior knowledge of Elastic and its various products and features are required, though basic system configuration, such as knowing how to run commands via a Linux based command line, and editing text files using a Unix based text editor (like Vim or Nano) is advantageous.
There is a Vim Tips section in this lab in case you need a little help or refresher to get the standard text editing accomplished.
Setup and requirements
Before you click the Start Lab button
Read these instructions. Labs are timed and you cannot pause them. The timer, which starts when you click Start Lab, shows how long Google Cloud resources will be made available to you.
This hands-on lab lets you do the lab activities yourself in a real cloud environment, not in a simulation or demo environment. It does so by giving you new, temporary credentials that you use to sign in and access Google Cloud for the duration of the lab.
To complete this lab, you need:
- Access to a standard internet browser (Chrome browser recommended).
- Time to complete the lab---remember, once you start, you cannot pause a lab.
How to start your lab and sign in to the Google Cloud console
-
Click the Start Lab button. If you need to pay for the lab, a pop-up opens for you to select your payment method. On the left is the Lab Details panel with the following:
- The Open Google Cloud console button
- Time remaining
- The temporary credentials that you must use for this lab
- Other information, if needed, to step through this lab
-
Click Open Google Cloud console (or right-click and select Open Link in Incognito Window if you are running the Chrome browser).
The lab spins up resources, and then opens another tab that shows the Sign in page.
Tip: Arrange the tabs in separate windows, side-by-side.
Note: If you see the Choose an account dialog, click Use Another Account. -
If necessary, copy the Username below and paste it into the Sign in dialog.
{{{user_0.username | "Username"}}} You can also find the Username in the Lab Details panel.
-
Click Next.
-
Copy the Password below and paste it into the Welcome dialog.
{{{user_0.password | "Password"}}} You can also find the Password in the Lab Details panel.
-
Click Next.
Important: You must use the credentials the lab provides you. Do not use your Google Cloud account credentials. Note: Using your own Google Cloud account for this lab may incur extra charges. -
Click through the subsequent pages:
- Accept the terms and conditions.
- Do not add recovery options or two-factor authentication (because this is a temporary account).
- Do not sign up for free trials.
After a few moments, the Google Cloud console opens in this tab.

Activate Cloud Shell
Cloud Shell is a virtual machine that is loaded with development tools. It offers a persistent 5GB home directory and runs on the Google Cloud. Cloud Shell provides command-line access to your Google Cloud resources.
- Click Activate Cloud Shell
at the top of the Google Cloud console.
When you are connected, you are already authenticated, and the project is set to your Project_ID,
gcloud is the command-line tool for Google Cloud. It comes pre-installed on Cloud Shell and supports tab-completion.
- (Optional) You can list the active account name with this command:
- Click Authorize.
Output:
- (Optional) You can list the project ID with this command:
Output:
gcloud, in Google Cloud, refer to the gcloud CLI overview guide.
Vim tips
- You can go to a specific line by entering the
:(colon sign), the line number, then the Enter key. - Use your arrows to move up, down, left, or right.
- Use the letter
xto remove letters or symbols, unless ininsertmode, where you will use the keyboard's normal delete/backspace keys. - Enter the letter
ito enter intoinsertmode where you will then be able to add/remove text. - Once your edit is complete press the
Esckey to exit out of insert mode, where you will then write/save the file by entering everything everything below, including the colon sign:
This is to say, you enter a : then wq which writes the file and quits the vim editor as soon as pressing the enter key.
Task 1. Create an Elastic deployment
Elasticsearch is a real-time, distributed storage, search, and analytics engine. It can be used for many purposes, but one context where it excels is indexing streams of semi-structured data, such as logs or decoded network packets.
In this section, you will first need to sign up for an Elastic free trial with your personal email address. You will then log into Elastic Cloud and create a deployment.
Create a deployment
- First, sign up for a free trial.
- Click Start free trial.
- Use your personal email, you'll need to go to your inbox to verify your email address.
You should be redirected to Elastic Cloud.
-
On the Create deployment page, give your deployment a name (i.e
my-lab-demo) and choose the closest Google Cloud region to you. -
Click Create Deployment.
-
Download or copy and save the password for the Elastic user, as you will use this later in the lab.
-
Once your deployment is ready, click Continue.
-
On the Welcome Page, click Explore on my own.
Task 2. Set up a service account
Google Cloud implements service accounts as a way to access APIs securely. To monitor Google Cloud with Elastic, you will need a service account. The easiest way is to use a predefined service account that Google Cloud creates automatically. Alternatively, you can create a new service account. In this lab, you will create a new one.
-
First, navigate to the Google Cloud Console. To access the service account menu, click Navigation Menu > IAM & Admin > Service Accounts.
-
Next, click Create Service Account. For the new service account name, use gcp-monitor. Optionally add a description (for example, "Service account to monitor Google Cloud services using the Elastic Stack"). Click Create and Continue.
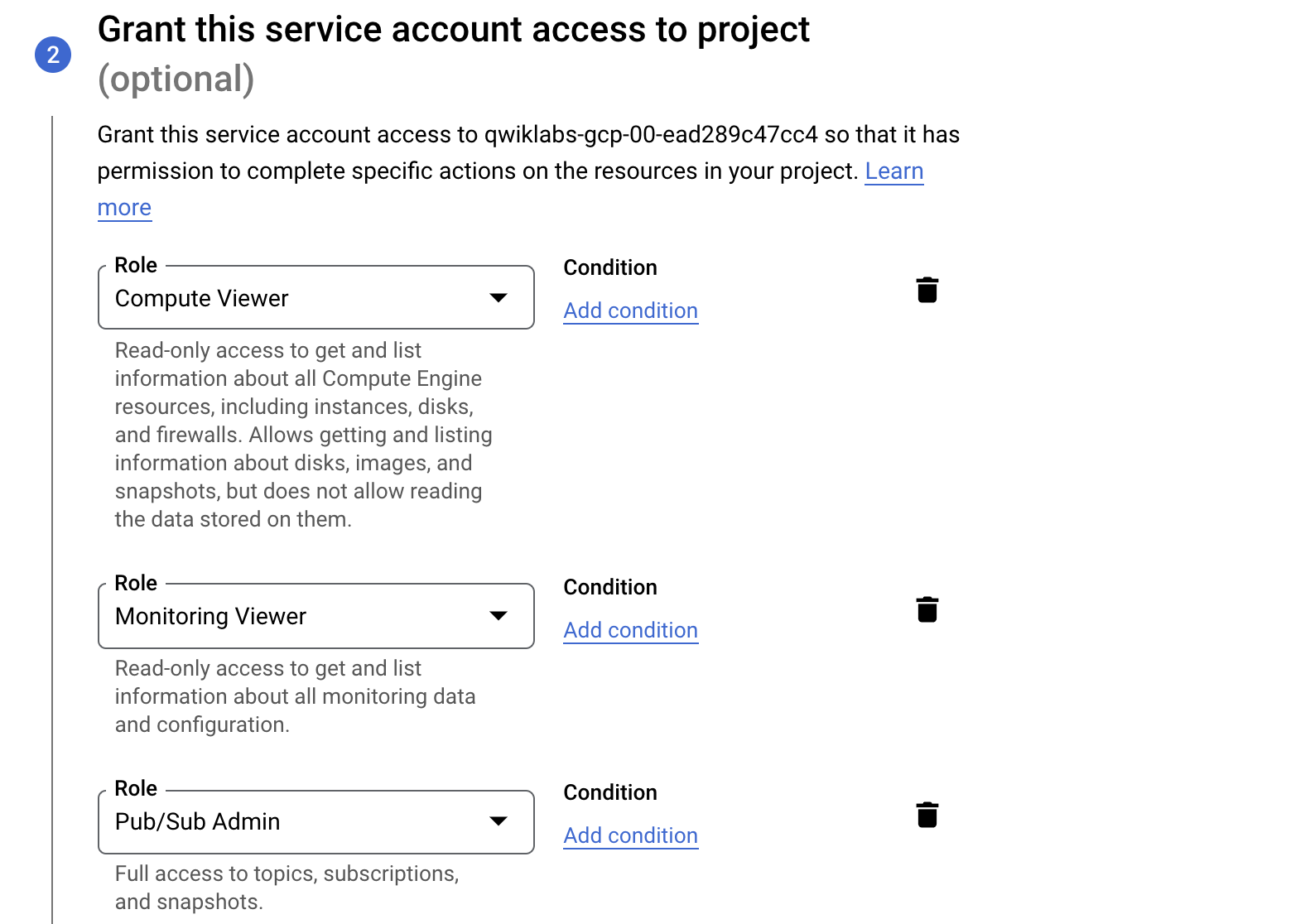
-
Next, add three main roles to the service account to monitor Google Cloud services:
- Compute Viewer
- Monitoring Viewer
- Pub/Sub Admin
-
Click Continue, then skip granting users access to this service.
-
Finally, click Done. The service account is now ready to be used.
-
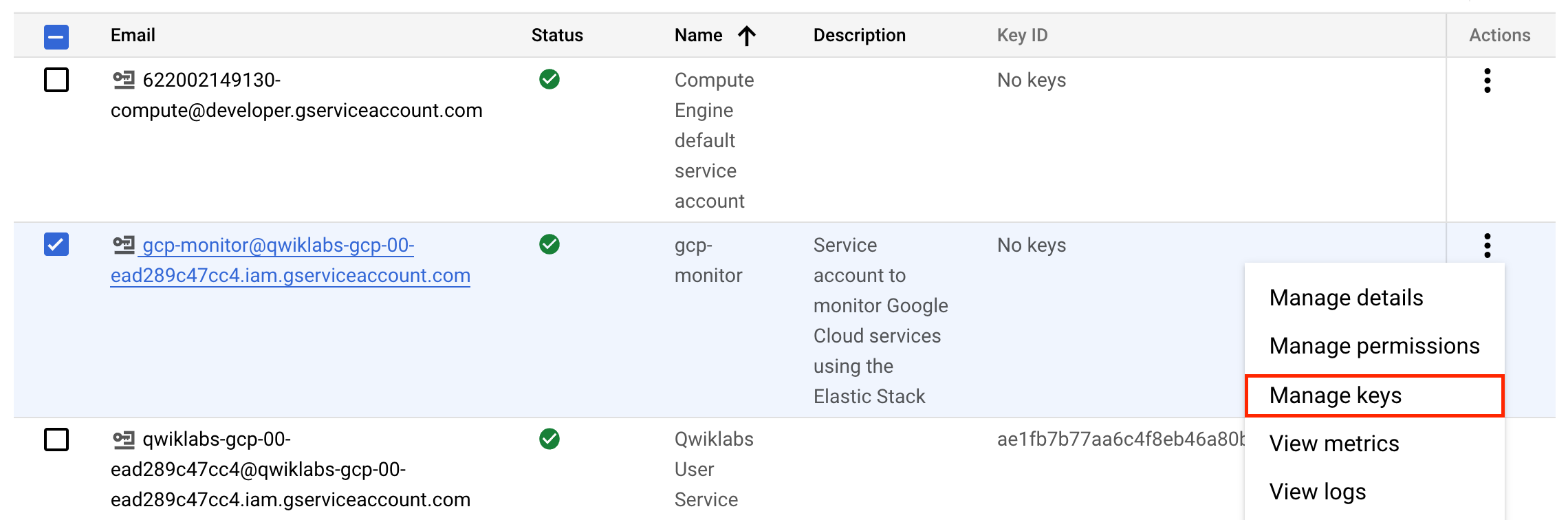
Next, to use the service account just created
gcp-monitor, click Manage keys.
-
On the Keys page, click Add Key > Create new key.
-
Select JSON as the type and click Create.
-
After clicking Create, the credential file is downloaded. Rename the file as credentials.json. Keep this file in an accessible place to use later.
-
Click Close.
Click Check my progress to verify the objective.
Task 3. Install beats
To monitor Google Cloud using the Elastic Stack, you need two main components: an Elastic deployment to store and analyze the data and an agent to collect and ship the data.
Two agents can be used to monitor Google Cloud:
- Metricbeat is used to monitor metrics
- Filebeat to monitor logs.
You can run the agents on any machine. For this lab, you will be using Cloud Shell.
Install Metricbeat
-
Navigate to Cloud Shell.
-
Download and install Metricbeat:
Set up assets
- Metricbeat comes with predefined assets for parsing, indexing, and visualizing your data. Run the following command to load these assets. It may take a few minutes.
username:password in this command. To find your Cloud ID, click on your deployment.
Configure Metricbeat output
Next, you are going to configure Metricbeat output to Elasticsearch Service.
- Use the Metricbeat keystore to store secure settings. Store the Cloud ID in the keystore:
To store metrics in Elasticsearch with minimal permissions, create an API key to send data from Metricbeat to Elasticsearch Service.
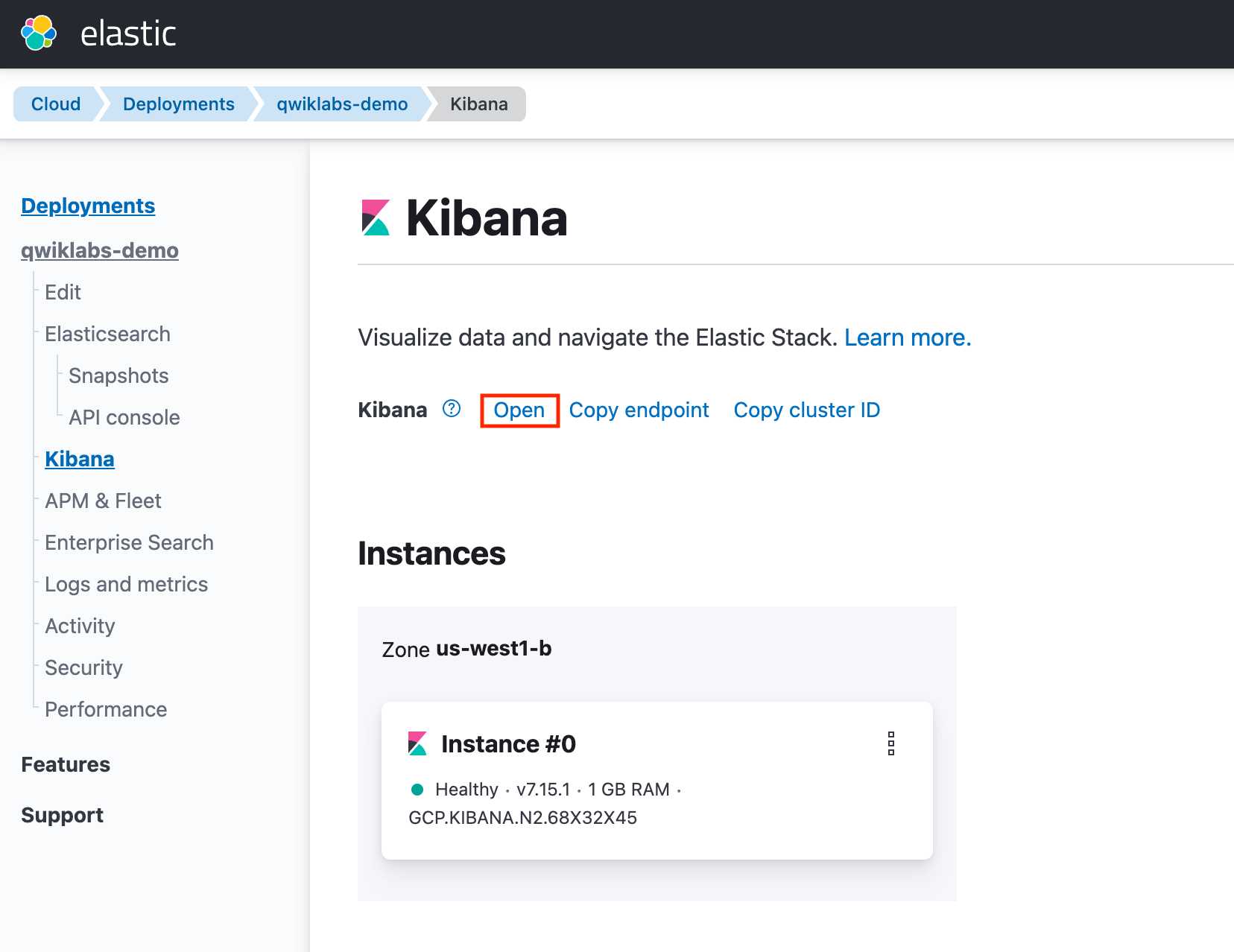
- Log into Kibana by navigating to your Elastic Cloud Deployments page and clicking Kibana on the left navigation menu.
-
Click Open.
-
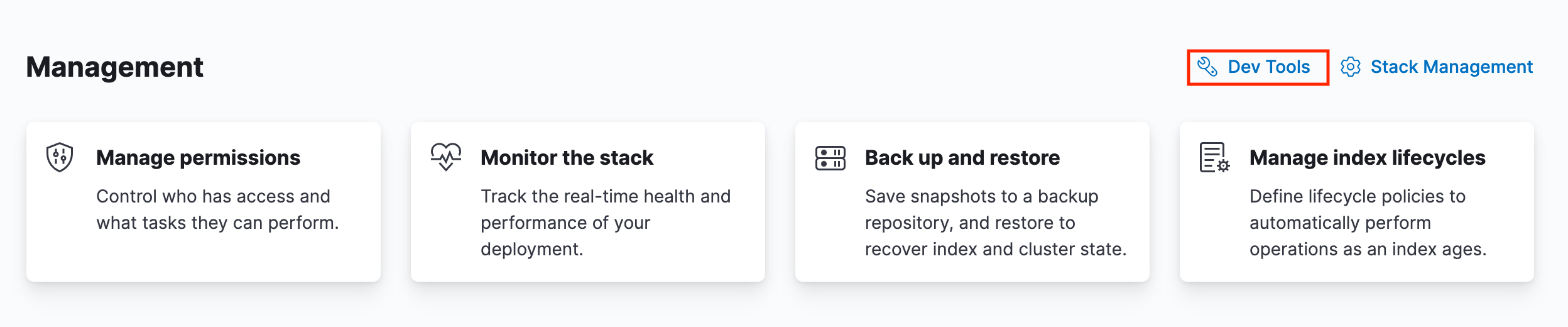
Select Management > Dev Tools.
- Send the following request. Click the play button to send the request:
- The response contains an
api_keyand anidfield, which can be stored in the Metricbeat keystore in the following format:id:api_key:
-n parameter; otherwise, you will have painful debugging sessions due to adding a newline at the end of your API key
- To see if both settings have been stored, run the following command:
- To configure Metricbeat to output to Elasticsearch Service, edit the
metricbeat.ymlconfiguration file. Add the following lines to the end of the file:
- Finally, test if the configuration is working. If it is not working, verify if you used the right credentials and add them again:
Now that the output is working, you are going to set up the input (Google Cloud).
Task 4. Configure Metricbeat Google Cloud Platform
To collect metrics from Google Cloud use the Google Cloud Platform module. This module periodically fetches monitoring metrics from Google Cloud Platform using Stackdriver Monitoring API for Google Cloud Platform services.
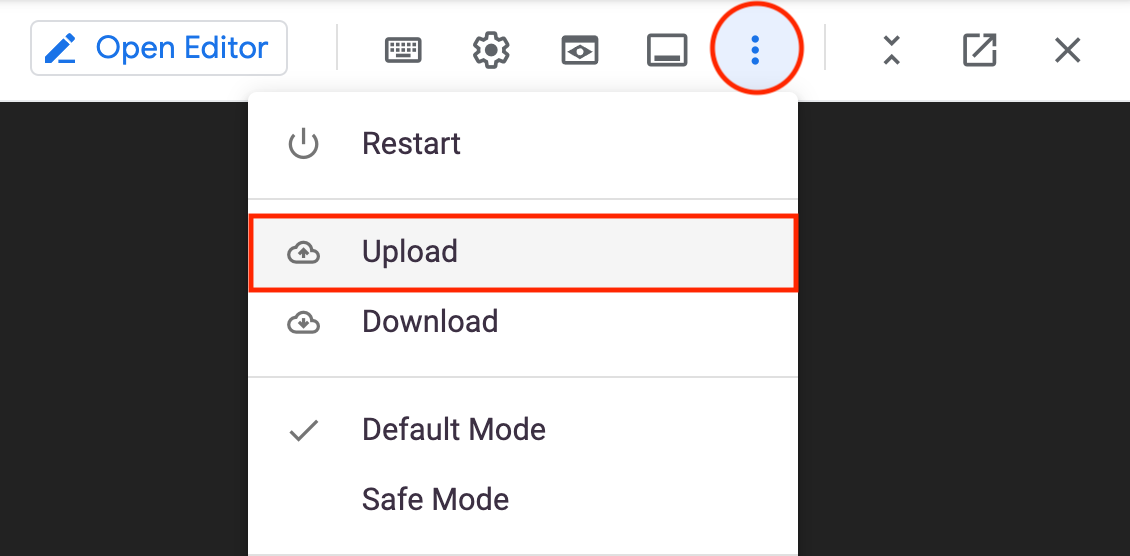
- From the Cloud Shell toolbar, click the three dots (
) on the navigation menu and select Upload.
-
Select your service account JSON key file (exported in the first section) and upload it to Cloud Shell. Note the location of the file as you will be using it in this section.
-
Next, run the following command to enable the Metricbeat GCP module.
-
Navigate to the metricbeat folder then
modules.d/gcp.ymlfile -
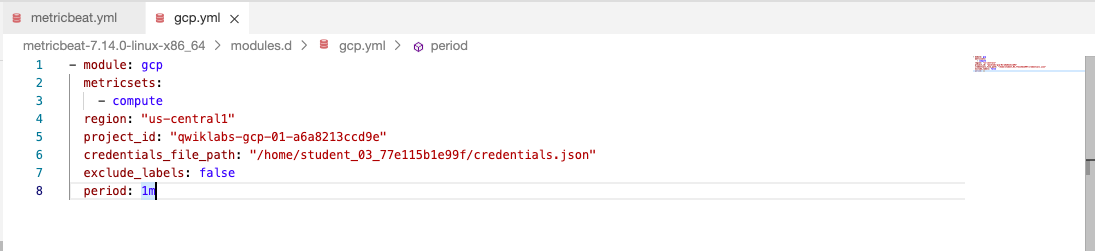
Replace the entire contents of the file with the following configurations. Make sure to replace
project_idandcredentials_file_pathwith the your correct values:
credentials.json is the file that you generated earlier.
Your file should resemble the following:
- To check if Metricbeat can collect data, test the input by running the following command:
Metricbeat will print Google Cloud metrics to the terminal, if the setup is correct.
- When the input and output are ready, start Metricbeat to collect the data:
- Finally, navigate back to Kibana and search for the [Metricbeat GCP] Compute Overview dashboard. Click the result to open the dashboard.
After a few minutes or so, your dashboard should resemble the following:
![The [Metricbeat GCP] Compute Overview dashboard](https://cdn.qwiklabs.com/QK0TisYYDE6I3Disu5FX4KXQk6QsmOJzneXq2BsDB6M%3D)
Task 5. Install Filebeat
Now that Metricbeat is up and running, configure Filebeat to collect Google Cloud logs.
- Open a new Cloud Shell tab, and run the following commands:
Set up assets
Filebeat comes with predefined assets for parsing, indexing, and visualizing your data.
- Run the following command to load these assets. It may take a few minutes.
username:password in this command. To find your Cloud ID, click on your deployment.
nginx_ecs or apache_ecs. It's safe to ignore these and continue on with the lab.
Configure Filebeat output
Next, configure Filebeat output to Elasticsearch Service.
- Use the Filebeat keystore to store secure settings. Store the Cloud ID in the keystore:
- To store logs in Elasticsearch with minimal permissions, create an API key to send data from Filebeat to Elasticsearch Service.
- Log into Kibana (you can do so from the Cloud Console without typing in any permissions).
- Open the left Navigation menu, scroll down and select Management > Dev Tools.
- Send the following request. Click the play button to send the request:
- The response contains an
api_keyand anidfield, which can be stored in the Filebeat keystore in the following format:id:api_key:
-n parameter; otherwise, you will have painful debugging sessions due to adding a newline at the end of your API key
- To see if both settings have been stored, run the following command:
- To configure Filebeat to output to Elasticsearch Service, edit the
filebeat.ymlconfiguration file. Add the following lines to the end of the file:
- Finally, test if the configuration is working:
Now that the output is working, you are going to set up the input (Google Cloud).
If it is not working, verify that you used the right credentials and, if necessary, add them again.
Task 6. Configure Filebeat Google Cloud module
To collect logs from Google Cloud, use the Google Cloud Platform module. This module periodically fetches logs that have been exported from Cloud Logging to a Pub/Sub topic sink. There are three available filesets: audit, vpcflow, firewall. This lab covers the audit fileset.
-
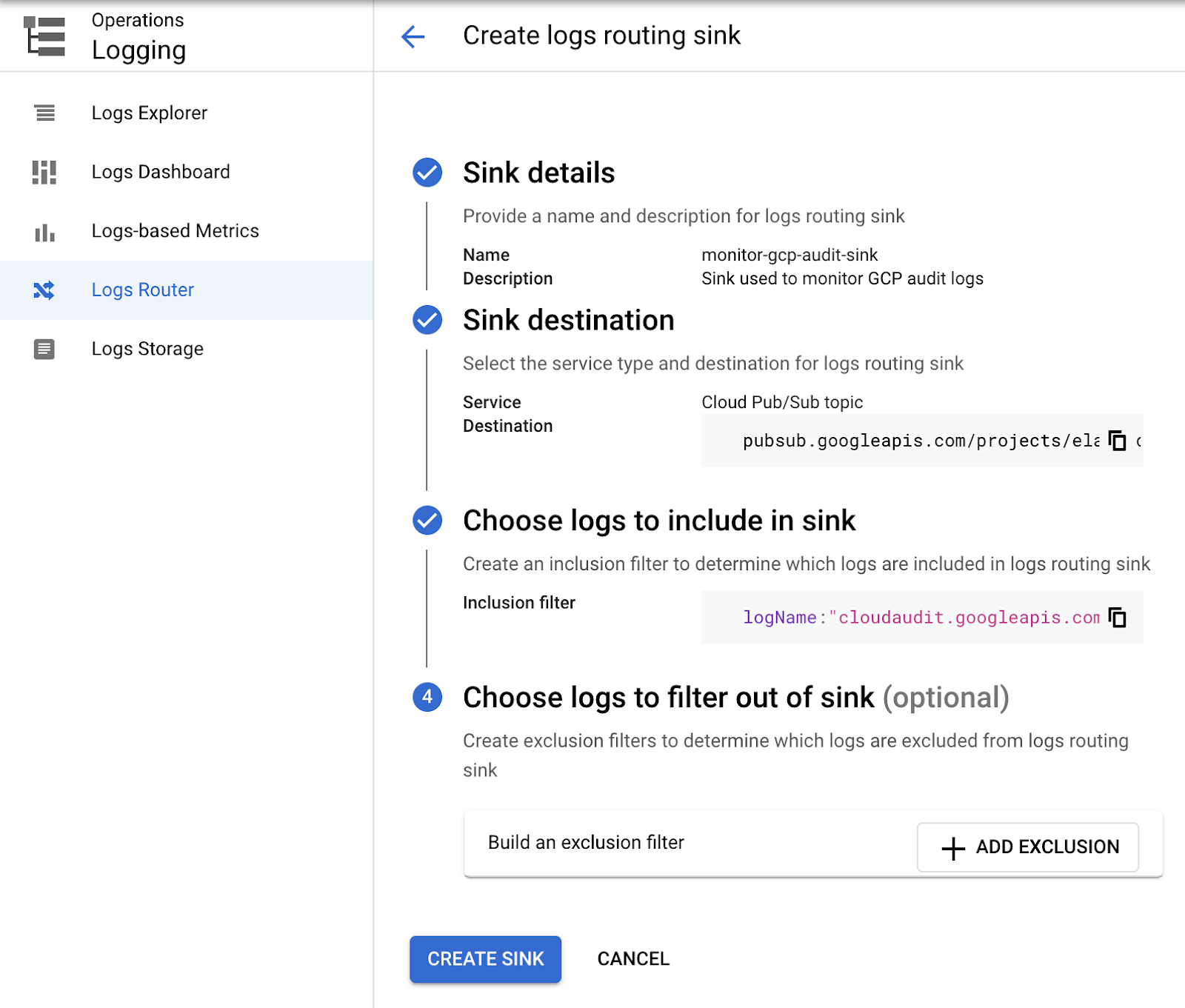
Use the search bar to find the Log Router page in Logging, where you'll configure Google Cloud to export logs to a Pub/Sub topic.
-
To set up the logs routing sink, click Create sink. Set sink name as
monitor-gcp-audit-sink. -
Click Next.
-
Under sink service select Cloud Pub/Sub topic and under select a cloud pub/sub topic click Create a Topic, enter
monitor-gcp-auditas Topic id, then click Create Topic. -
Click Next.
-
Finally, under Choose logs to include in sink, add
logName:"cloudaudit.googleapis.com"(it includes all audit logs). -
Click Create Sink. It will look something like the following:
Click Check my progress to verify the objective.
- Now that Google Cloud is configured to export audit logs, run the following to enable the Filebeat Google Cloud module:
-
Navigate to the filebeat folder then to
modules.d/gcp.ymlfile. -
Replace the entire contents of the file with the following configurations. Make sure to update
var.project_idandvar.credentials_filewith the your correct values:
- Start Filebeat to collect the logs:
- Finally, log into Kibana and open the [Filebeat GCP] Audit dashboard.
After a few minutes, you should see incoming data in the dashboard.
Click Check my progress to verify the objective.
Congratulations!
In this lab you created a deployment using Elastic Cloud, installed and configured Beats to send data to Elasticsearch, then finally used Kibana to visualize the ingested data.
Next steps / Learn more
- Elastic on the Google Cloud Marketplace!
- Elastic Cloud offers a fully managed experience so that you can focus on your data instead of managing the cluster. You can check it out here and play with a free trial.
- Check out the Elastic Integrations page and see how easily you can stream in logs, metrics, traces, content, and more from your apps, endpoints, infrastructure, cloud, network, workplace tools, and every other common source in your ecosystem.
- Leverage the out-of-the-box solutions to give your Elastic project a jump start!
Google Cloud training and certification
...helps you make the most of Google Cloud technologies. Our classes include technical skills and best practices to help you get up to speed quickly and continue your learning journey. We offer fundamental to advanced level training, with on-demand, live, and virtual options to suit your busy schedule. Certifications help you validate and prove your skill and expertise in Google Cloud technologies.
Manual Last Updated: November 08, 2024
Lab Last Tested: November 08, 2024
Copyright 2024 Google LLC All rights reserved. Google and the Google logo are trademarks of Google LLC. All other company and product names may be trademarks of the respective companies with which they are associated.

![The compute overview search results with '[Metricbeat GCP] Compute Overview' selected](https://cdn.qwiklabs.com/c24d5EsScYmne2iM7eNibFkH3hJ0zJmvc5nbq1m2fEw%3D)
![The [Filebeat GCP] Audit dashboard](https://cdn.qwiklabs.com/AknN40I2K%2FvnWuwkmnDd5MBR2ciH1vW27JFxpEvvySk%3D)

